Table Of Contents
-
FedRAMP 20x is Already Impacting Current Rev 5 Efforts
-
The Decision Is No Longer Just “Rev 5 or 20x”
-
Should You Wait for FedRAMP 20x?
-
What the FedRAMP 20x Model Actually Requires
-
Is Pursuing FedRAMP Rev 5 a Waste of Money?
-
Will FedRAMP 20x Require a Massive Overhaul?
-
Preparing for 20x While Pursuing Rev 5
-
Moving from Rev 5 to 20x
-
What to Consider When Deciding Between Rev 5 and 20x
-
Making the Decision
-
Stay Current
The federal cloud security landscape is undergoing one of its most significant shifts in years with the introduction of FedRAMP 20x. As of publication date 30 March 2026, the Project Management Office (PMO) is moving through the second phase of its pilot program, and cloud service providers (CSPs) are facing a very practical decision:
Do you continue pursuing Rev 5, or do you wait for FedRAMP 20x?
This isn’t just a timing question. It’s also a question of how you want to build, because the real shift happening underneath FedRAMP is this:
Rev 5 is built around audit-day proof. 20x is built around everyday proof.
That distinction shows up everywhere: in how systems are evaluated, how security is demonstrated, and how much of your program has to actually work versus be explained.
Let’s walk through what that shift means and how to think about your path forward.
If you’re looking for additional context along the way, we’ve also put together a FedRAMP 20x resource hub with both plain-English explainers and deeper technical content.
FedRAMP 20x is Already Impacting Current Rev 5 Efforts
For companies currently pursuing Rev 5 adoption, FedRAMP 20x represents both a challenge and an opportunity.
The most immediate impact is the timeline: All authorizations, whether achieved through 20x or legacy Rev 5 processes, are expected to transition to 20x-style continuous reporting requirements in late 2027 or early 2028. Low and moderate systems are expected to transition first, followed by high impact systems approximately six months later.
This means that investing in Rev 5 today doesn’t eliminate the need to prepare for 20x: It simply delays when you deal with it.
On the other hand, companies pursuing Rev 5 will still need to implement the core pillars of 20x:
- Key Security Indicators (KSIs)
- Vulnerability Detection and Response (VDR)
- Significant Change Notification (SCN)
- Minimum Assessment Scope (MAS)
The underlying controls remain the same. What changes is how they are demonstrated: In a Rev 5 world, documentation explains reality. In a 20x world, systems show reality.
And when systems start showing reality continuously, weaknesses get exposed faster. That’s the real shift.
If you want a deeper breakdown of that difference, see our technical breakdown of FedRAMP 20x vs Rev 5.
The Decision Is No Longer Just “Rev 5 or 20x”
The framing above is why the conversation is no longer just “Rev 5 or 20x.”
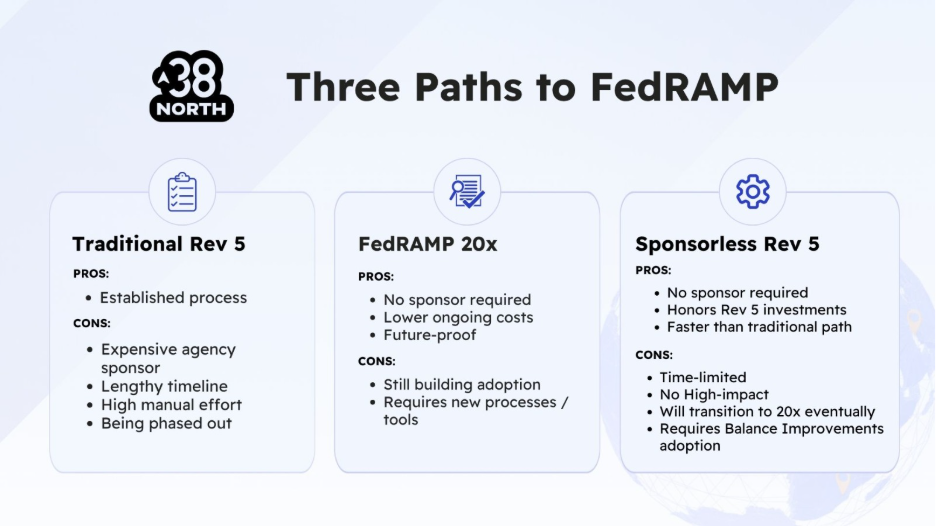
In practice, there are three paths that teams are evaluating today:
- Traditional Rev 5
- FedRAMP 20x
- Sponsorless Rev 5
Each comes with a different balance of:
- timing
- sponsorship requirements
- implementation effort
- and how directly it aligns with the eventual shift to 20x
Should You Wait for FedRAMP 20x?
The decision to wait for 20x versus pursuing Rev 5 now depends heavily on your current circumstances and business needs.
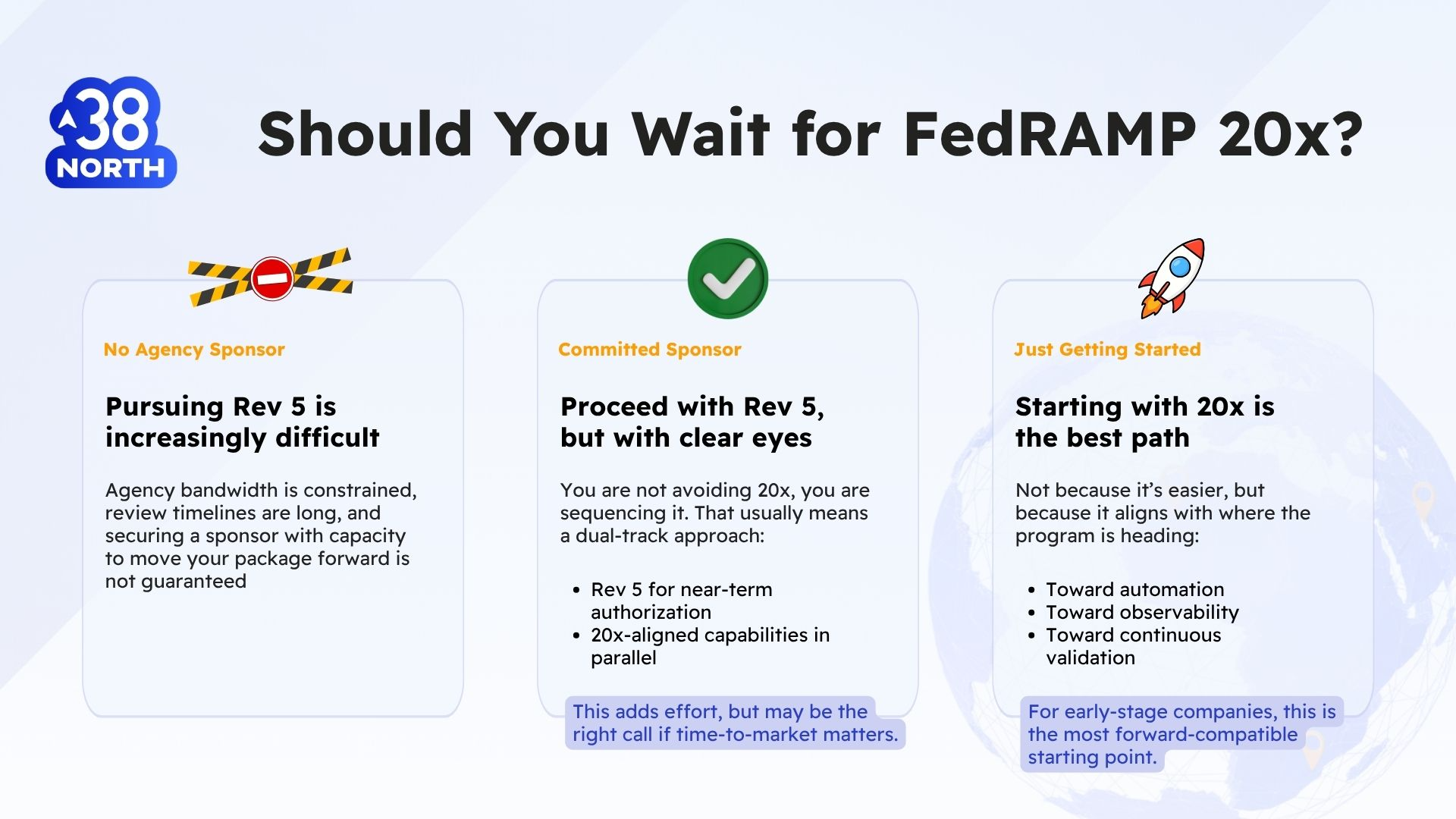
If you don’t have an agency sponsor:
Pursuing Rev 5 is increasingly difficult. Agency bandwidth is constrained, review timelines are long, and securing a sponsor with capacity to move your package forward is not guaranteed.
In this case, waiting for, or aligning to, 20x may be the more strategic move.
If you have a committed sponsor:
You can proceed with Rev 5, but you should do it knowing that you are not avoiding 20x: You are sequencing it. That usually means running a dual-track approach:
- Rev 5 for near-term authorization
- 20x-aligned capabilities in parallel
This adds effort, but it may be the right decision if time-to-market matters.
If you’re just getting started:
For companies early in their FedRAMP journey, starting with 20x is the best path.
Not because it’s easier, but because it aligns with how the program is moving:
- toward automation
- toward observability
- toward continuous validation
If helpful, we break this down further in our plain-English overview of FedRAMP 20x.
What the FedRAMP 20x Model Actually Requires
The 20x rollout follows a structured pilot process and is currently (as of publication date 30 March 2026) refining low moderate-level requirements and a new “class” called “Class A” that focuses on marketplace participation in the 20x program before broader implementation.
At its core, the model centers on four core components:
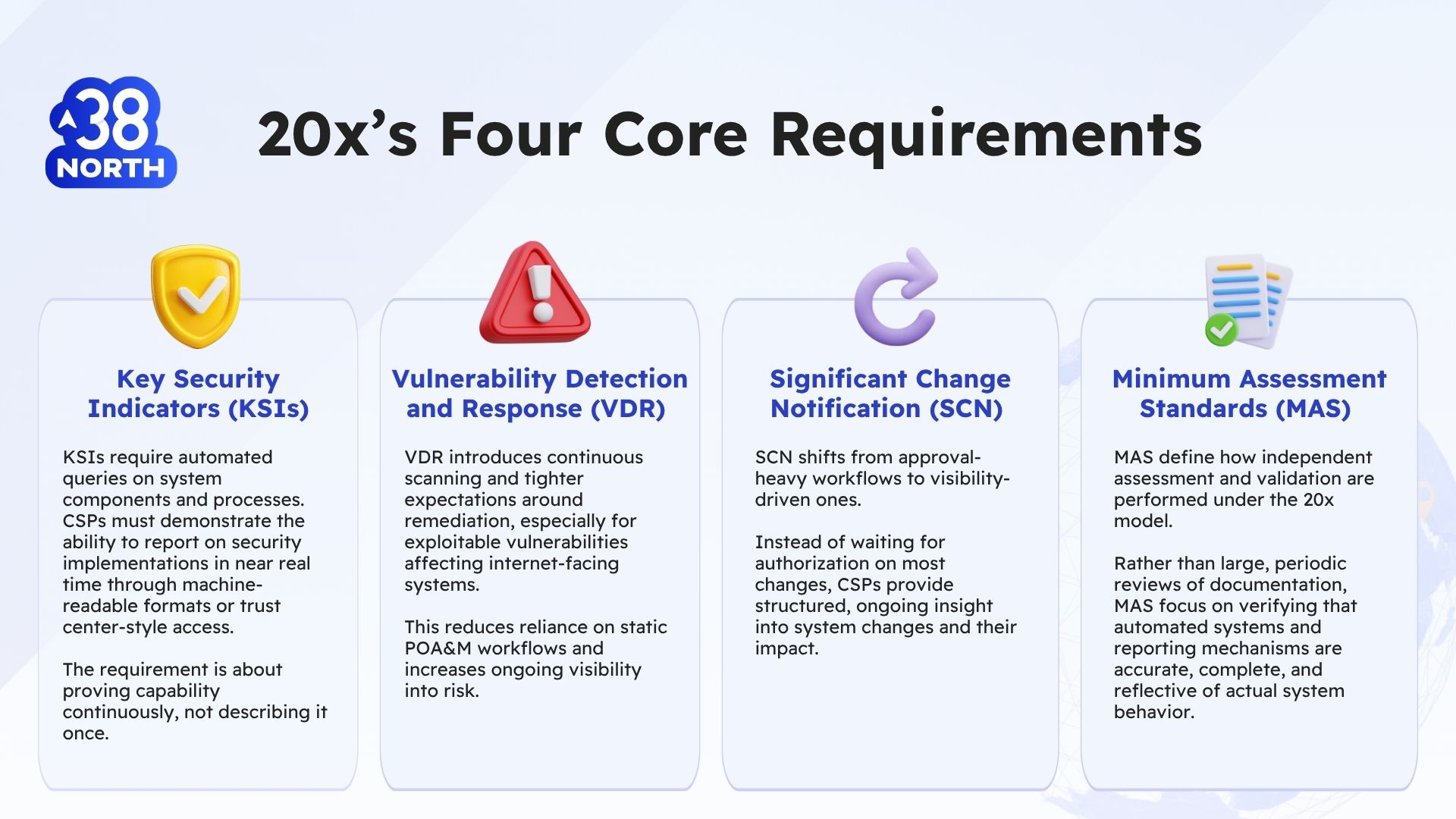
Key Security Indicators (KSIs)
KSIs require automated queries on system components and processes. CSPs must demonstrate the ability to report on security implementations in near real time through machine-readable formats or trust center-style access.
The requirement is about proving capability continuously, not describing it once.
Vulnerability Detection and Response (VDR)
VDR introduces continuous scanning and tighter expectations around remediation, especially for exploitable vulnerabilities affecting internet-facing systems.
This reduces reliance on static POA&M workflows and increases ongoing visibility into risk.
Significant Change Notification (SCN)
SCN shifts from approval-heavy workflows to visibility-driven ones.
Instead of waiting for authorization on most changes, CSPs provide structured, ongoing insight into system changes and their impact.
Minimum Assessment Scope (MAS)
MAS define how independent assessment and validation are performed under the 20x model.
Rather than large, periodic reviews of documentation, MAS focus on verifying that automated systems and reporting mechanisms are:
- accurate
- complete
- and reflective of actual system behavior
This shifts assessment away from point-in-time artifact review and toward validating that continuous evidence is trustworthy.
MAS ensure that what you’re reporting continuously is available and credible. Across all these, the pattern is consistent: Less audit theater. More operational truth.
Is Pursuing FedRAMP Rev 5 a Waste of Money?
This is one of the most common, and most nuanced, questions.
From a pure efficiency standpoint, investing heavily in documentation and manual processes that will need to evolve within a few years can create duplication.
But that doesn’t make Rev 5 the wrong choice.
There are valid reasons to pursue it:
- Market access timing: You need federal customers now.
- Sponsor relationships: You have a committed agency partner.
- Other frameworks: Some programs will continue relying on Rev 5-style approaches.
FedRAMP is also introducing Balance Improvement Releases, which allow CSPs to adopt elements of the 20x model incrementally, even as they continue complying with Rev 5.
In addition, sponsorless Rev 5 paths provide an option for companies that have done significant work toward Rev and lost their sponsorship, or had contracts cancelled that required a Rev 5 authorization.
The key is how you approach it. Rev 5 is not a waste if it builds toward 20x. It becomes wasteful if it delays it.
Will FedRAMP 20x Require a Massive Overhaul?
That depends on how your system is built today. For organizations heavily invested in supporting manual documentation, point-in-time evidence, or fragmented tooling, the shift will be significant.
You’ll need to:
- build automated security signal validations and reporting
- implement continuous monitoring
- create machine-readable outputs or trust center interfaces
- establish change visibility systems
But for organizations already investing in telemetry, configuration monitoring, or centralized logging, the transition is less about rebuilding and more about connecting.
The real requirement is: Your system needs to be able to show what is true—continuously.
Preparing for 20x While Pursuing Rev 5
For companies currently implementing Rev 5, preparation for 20x should happen in parallel.
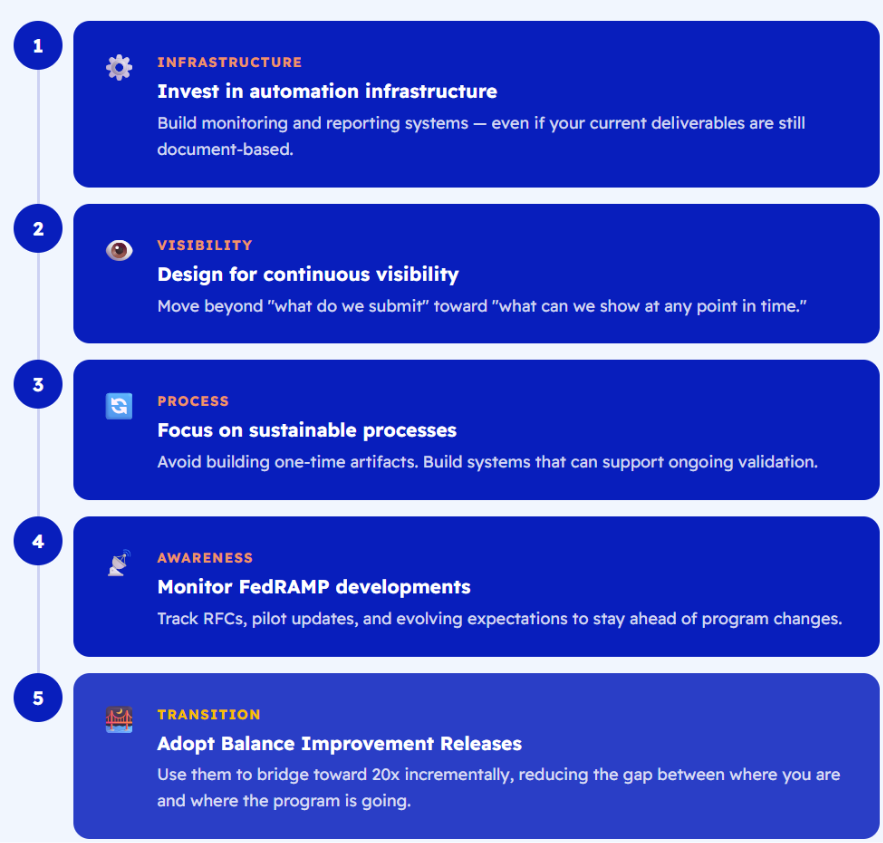
Invest in automation infrastructure
Build monitoring and reporting systems, even if your current deliverables are still document-based.
Design for continuous visibility
Move beyond “what do we submit” toward “what can we show at any point in time.”
Focus on sustainable processes
Avoid building one-time artifacts. Build systems that can support ongoing validation.
Monitor FedRAMP developments
Track RFCs, pilot updates, and evolving expectations.
Adopt Balance Improvement Releases
Use them to bridge toward 20x incrementally.
For more detail, see how to prepare for continuous validation under FedRAMP 20x.
Moving from Rev 5 to 20x
The transition from Rev 5 to 20x is less about rewriting documentation and more about changing how security is expressed.
Rev 5:
- explains security through documentation
- validates it periodically
20x:
- demonstrates security through system reporting
- validates it continuously
Instead of describing your controls, you show their current state. And instead of submitting reports, you provide ongoing visibility. The controls themselves don’t change. The expectation does.
What to Consider When Deciding Between Rev 5 and 20x
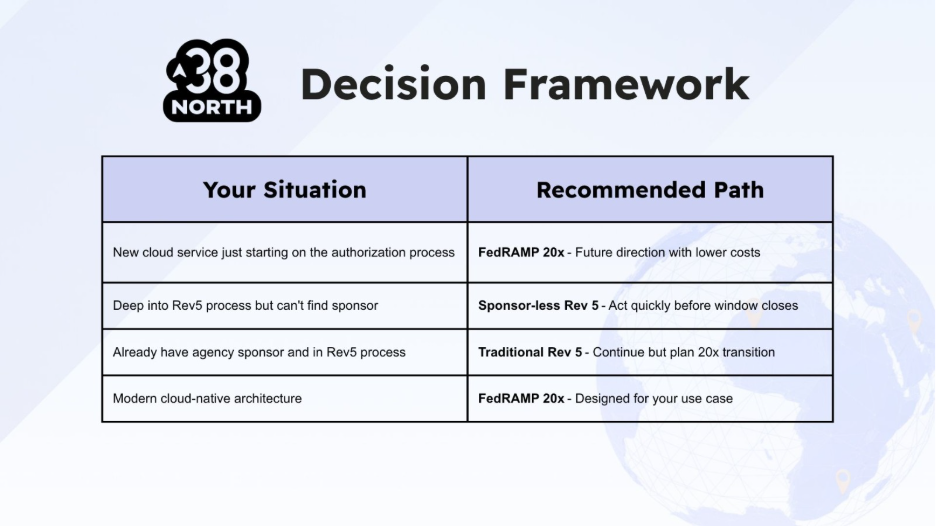
The framework above summarizes how different starting points typically map to different paths:
- New cloud services → often align more naturally with 20x
- Teams deep in Rev 5 without sponsors → may consider sponsorless options
- Sponsored Rev 5 efforts → often continue, with 20x preparation in parallel
Talk to us about the best path for your situation.
Making the Decision
Ultimately, choosing between Rev 5 and 20x is a business decision.
It depends on:
- your timeline
- sponsor availability
- technical maturity
- resource capacity
But the direction of the program is clear: FedRAMP is moving from audit-day proof to everyday proof. The sooner your system reflects that reality, the better positioned you’ll be, whether you pursue Rev 5 first or align directly to 20x.
Stay Current
For ongoing updates, you can follow:
- FedRAMP community discussions
- PMO GitHub project board
And for practical guidance, examples, and deeper dives, explore our FedRAMP 20x resource hub.
Table Of Contents
-
FedRAMP 20x is Already Impacting Current Rev 5 Efforts
-
The Decision Is No Longer Just “Rev 5 or 20x”
-
Should You Wait for FedRAMP 20x?
-
What the FedRAMP 20x Model Actually Requires
-
Is Pursuing FedRAMP Rev 5 a Waste of Money?
-
Will FedRAMP 20x Require a Massive Overhaul?
-
Preparing for 20x While Pursuing Rev 5
-
Moving from Rev 5 to 20x
-
What to Consider When Deciding Between Rev 5 and 20x
-
Making the Decision
-
Stay Current






