As Japan accelerates its adoption of cloud technologies across government agencies, the Information System Security Management and Assessment Program (ISMAP) has emerged as a cornerstone of its cloud security framework since its inception in June 2020.
The program is governed and supported by several key government entities, including:
- The Cabinet Secretariats of the National Cybersecurity Office (NSO);
- The Digital Agency (DA);
- The Ministry of Internal Affairs and Communications (MIC);
- The Ministry of Economy, Trade and Industry (METI);
- The ISMAP Steering Committee, which administers the framework and sets regulations and requirements; and
- The Information Technology Promotion Agency (IPA), which operationally and technically supports the ISMAP Steering Committee.
ISMAP serves as a centralized evaluation and regis-tration framework ensuring that cloud service providers (CSPs) meet a unified, government-approved baseline of security. By establishing a single, common security bar, ISMAP streamlines how government organizations assess cloud platforms and reinforces trust in the digital services supporting public-sector operations.
The framework is built around several foundational documents that guide CSPs through the registration process and lay out the security expectations required for approval. These include the ISMAP Management Standards and the Cloud Service Registration Rules, which describe the procedures and responsibilities tied to becoming an approved provider.
For SaaS solutions supporting lower-risk government use cases, ISMAP-LIU (Low-Impact-Use) was introduced in 2022. ISMAP-LIU is a streamlined extension of the ISMAP framework that reduces the assessment complexity, documentation requirements, and encompasses a slightly narrower scope while maintaining security rigor for services that do not process sensitive or confidential government information. This allows for a more efficient adoption of cloud SaaS solutions across various Japanese government agencies with needs.
What distinguishes ISMAP is its strong alignment with international and Japanese security standards.
Its Controls Criteria consolidate requirements from globally recognized frameworks like:
- ISO/IEC 27001;
- ISO/IEC 27017;
- ISO/IEC 27014; and
- NIST SP 800-53, rev. 5.
These sources—combined with Japanese-specific standards such as JIS Q 27001—form a unified, comprehensive baseline that CSPs must meet in order to demonstrate secure practices. By drawing from these established standards, ISMAP leverages mature, globally vetted guidance while tailoring it to Japan’s public sector needs.
In practice, ISMAP is far more than a compliance checklist. It’s a government-wide mechanism for ensuring that cloud services are designed, managed, and monitored in ways that protect sensitive government information. Agencies may also impose additional requirements on top of ISMAP registration, but the program itself is the minimum expectation. For CSPs seeking to support the Japanese government, ISMAP is both a gateway and a long-term security commitment.
Inside ISMAP’s Governance, Management, and Controls Criteria
The heart of ISMAP lies within its three core criteria: Governance, Management, and Controls. Each of these criteria reflects a different dimension of security maturity that CSPs must demonstrate before they can be registered for government procurement. The Governance and Management Criteria are mandatory requirements and failure to meet even a single requirement can be considered a registration blocker. Together, they ensure that a provider’s security posture is rooted in leadership oversight, organizational accountability, and a well-refined compliance posture to deliver a secure and effective cloud service offering (CSO).
The Governance Criteria focuses on establishing strong, organization-wide security foundations. CSPs must demonstrate risk-based decision-making, maintain clear direction for security investments, and meet internal and external compliance obligations. A strong security culture is also essential. Leadership is expected to promote awareness, accountability, and alignment between information security and corporate governance. Ultimately, the ISMAP Steering Committee wants to see that security is not merely operational—it must be embedded into the organization’s strategic mindset.
The Management Criteria, based on JIS Q 27001, guide CSPs in building and maintaining an effective ISMS. This includes documentation practices, risk management, communication protocols, and continuous improvement processes. ISMAP expects CSPs to demonstrate not only that these systems exist on paper but that they are actively operated, reviewed, and optimized over time. This requirement aligns with the philosophy of ISO/IEC 27001 ensuring that security is an ongoing lifecycle, not a one-time certification.
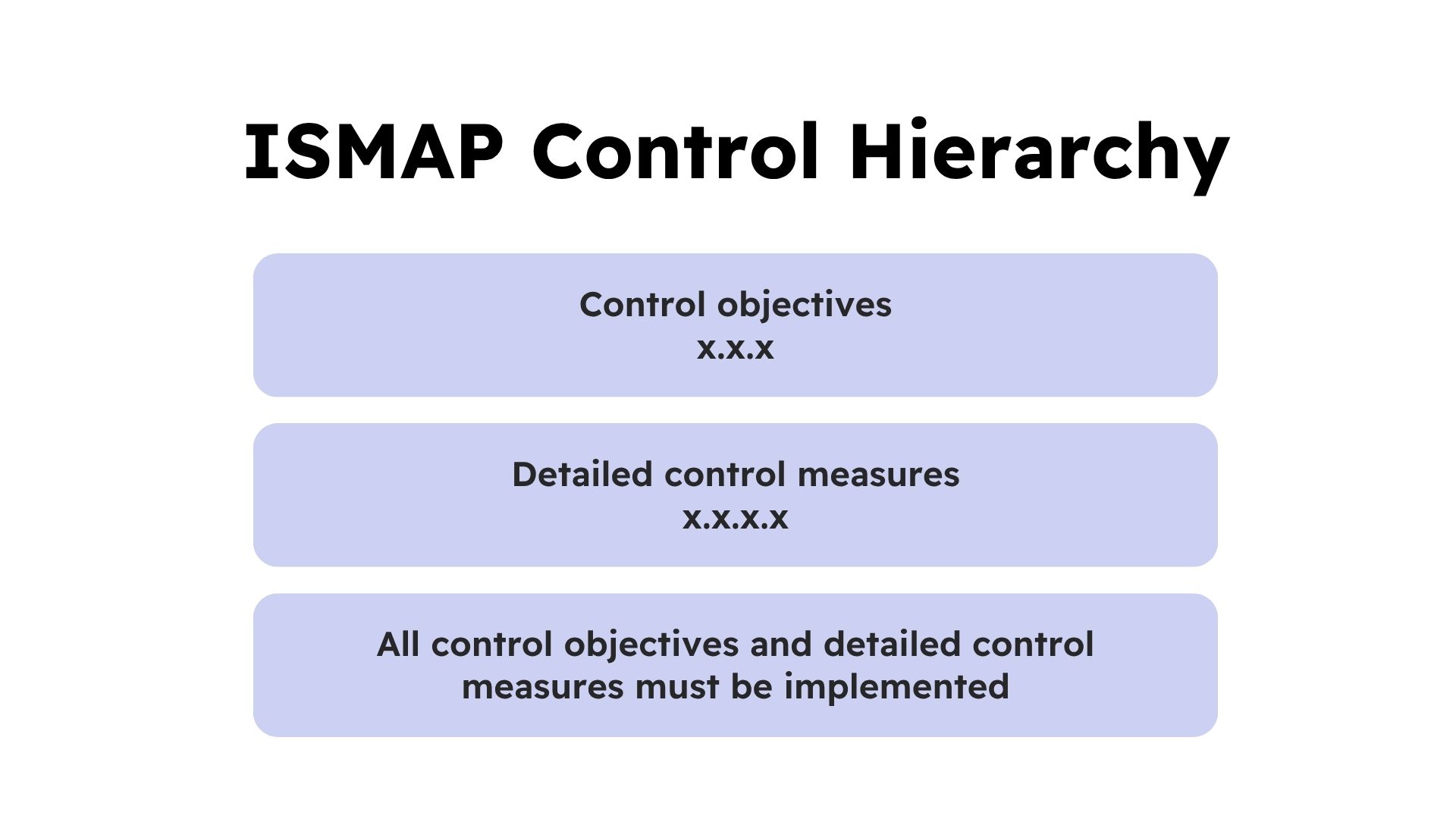
Finally, the Controls Criteria define the specific security measures CSPs must implement. These include organizational, human resources, IT operations, physical, technical, and cloud-specific controls modeled on consolidated international standards. Each requirement is structured around high-level control objectives (three-digit codes) and detailed implementation measures (four-digit codes). CSPs are expected to implement all controls unless a risk-based justification makes a specific item inapplicable. This structure provides both consistency and flexibility while ensuring that government data—typically treated as confidential—remains protected across the lifecycle of cloud operations.
Overlaps Among ISMAP, ISO 27001, and FedRAMP
The core overlaps among ISMAP, FedRAMP, and ISO 27001 stem from their shared goal of establishing a rigorous, standardized approach to securing cloud environments and safeguarding sensitive information. Although each framework was developed by different authorities and serves different regulatory needs, they converge around common principles such as risk management, structured governance, compliant operations, and comprehensive technical controls. Together, they emphasize consistent themes like access control, logging and monitoring, incident response, configuration management, and vulnerability handling—forming a unified security foundation that spans international, U.S., and Japanese government requirements.
- Risk & ISMS backbone:
- ISMAP requires an ISMS aligned with JIS Q 27001 and JIS Q 27017 (much like ISO/IEC 27001). Formalization of risk management starting with the cloud service provider down to the product offering are derived from both ISO and FedRAMP standards and requirements.
- Common control themes:
- Access control & identity
- Logging/monitoring & audit
- Configuration & change management
- Vulnerability management & patching
- Incident response & continuity
- Physical & personnel security
- Supplier/third-party risk
Where ISMAP Most Overlaps
- With ISO 27001: Governance and management criteria (based on ISO/IEC 27001, 27002, 27014) + cloud-specific controls from ISO/IEC 27017; ISMAP uses control objectives (X.X.X) and detailed control measures (X.X.X.X) with risk-based exceptions.
- With FedRAMP: ISMAP incorporates NIST SP 800-53 Rev. 5 concepts in its Controls Criteria for cloud-specific controls not addressed by ISO. Both frameworks require formal assessment and government acceptance (ISMAP-Registration vs. FedRAMP ATO), structured documentation (ISMAP application & assessment reports vs. FedRAMP SSP Package), and ongoing control of operations and maintenance.
ISMAP’s Distinguishing Features
- ISMAP: Japan government procurement baseline; governance + management criteria must be implemented; cloud-specific depth (ISO 27017 + FedRAMP Moderate control concepts).
- FedRAMP: U.S. government ATO process using NIST SP 800-53 security control baselines (Low/Moderate/High + overlays), continuous monitoring, Third-Party Assessment Organization (3PAO) assessments.
- ISO/IEC 27001: International ISMS certification standard; flexible control selection using Annex A (2022’s 93 controls across Organizational, People, Physical, and Technological themes).
How Can 38North Security Help You with your ISMAP Journey?
To support you throughout your ISMAP journey, we provide end‑to‑end guidance across the entire lifecycle—from initial planning and readiness through formal assessment and ultimately registering your CSO for ISMAP‑Registration. Our approach includes preparing you for a Readiness Assessment, offering advisory and consultation services with ISMAP‑Registered Auditors, and translating audit findings into a clear roadmap to guide remediation and implementation efforts.
Our advisory support extends to documentation development, evidence preparation, and internal audit activities to ensure full alignment with ISMAP’s framework and programmatic requirements before entering the formal assessment. Because the ISMAP assessment can be lengthy and complex depending on your scope and internal resourcing, 38North provides targeted consultation to help drive a successful outcome and smooth navigation of the ISMAP Steering Committee’s Registration Examination.
We also help bridge any language barriers between Japanese and English to ensure the process remains seamless. Once approved and listed on the ISMAP Cloud Service List, we continue to support you through ongoing monitoring and annual requirement reassessments to keep pace with the evolving ISMAP program.
Are you ready for your ISMAP journey? Get in touch with our team.
Stay tuned for Part 2, where we’ll explore the proposed changes expected to take effect in March 2027.
Sources:
- ISMAP Overview: https://www.ismap.go.jp/csm?id=kb_article_view&sysparm_article=KB0010301&sys_kb_id=a00cd78a2b5fa250f0bbfd69fe91bf93&spa=1
- Basic Regulations for ISMAP:
- ISMAP Management Standards: https://www.ismap.go.jp/csm?id=kb_article_view&sys_kb_id=da947d9e2bf9fa90f0bbfd69fe91bfa4
- ISMAP Cloud Service Registration Rules: https://www.ismap.go.jp/sys_attachment.do?sys_id=fc0c9b8a2b5fa250f0bbfd69fe91bf0b






