A cyber security incident can cause significant damage to an organization. It will wreak havoc on an environment and cost time, money, and diminish reputations. According to IBM’s Cost of a Data Breach Report 2021, the average cost of a breach was an outstanding $3.61 million dollars. 38% of that cost was due to lost business.
Another incredible finding in this report is that organizations that formed and tested an incident response plan saw an average total cost that was $2.46 million less that organizations that did not. Developing an effective incident response plan can greatly optimize response times and reduce all costs associated with an incident.
What is an incident response plan?
In its simplest form it is a plan with a set of instructions to guide an organization through all steps of incident response. These steps usually include preparation, detection, analysis, containment, eradication, recovery, and post-incident activity. The incident response plan can help an organization develop, maintain, and evolve their incident response capabilities.
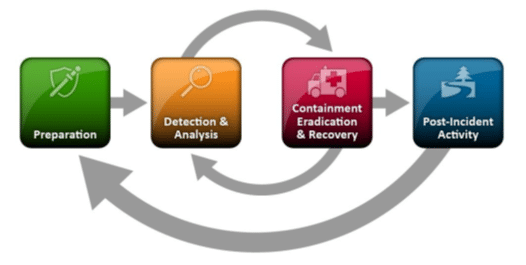
A four phase approach to incident response planning
The National Institute of Standards and Technology (NIST) highlights Preparation, Detection and Analysis, Containment, Eradication and Recovery, and Post-Incident Activity as the four key phases of Incident response. These should be detailed in the incident response plan for the organization.
Preparation
The preparation phase is the foundation for the remaining phases and is focused on establishing an incident response capability. This includes identifying and training dedicated personnel for incident response, configuring the environment for detection and prevention of potential incidents, and educating users on incident response and reporting procedures.
Detection & Analysis
Detection is one of the most challenging parts of incident response for an organization. In 2021, it took an average of 287 days to identify and contain a data breach. For the detection phase in the incident response plan, specific processes and tools should be identified to monitor, detect, and alert on suspicious activity. This should include an incident reporting and tracking system to track an incident throughout the remaining phases and then archived for future reference. Analysis of a potential incident should have processes and procedures identified to determine the scope and severity of the incident and ways to collect, store, and preserve the data in relation to the incident.
Containment, Eradication & Recovery
The goal of containment is to stop the effects of the incident before it can cause any further damage. Tactics and techniques for containment will vary based on the type of incident, and maturity level of the incident response capabilities. Typical containment activities include system isolation, updating firewall filters, and resetting system credentials. The eradication and recovery objective is to return to normal operations as safely as possible. Eradication and recovery plans are also dependent upon the incident type, and incident response capabilities. These plans should offer processes and procedures for system remediation, system restoration, and vulnerability management.
Post-Incident Activity
Post-incident activity is a critical, and yet easily overlooked phase. The plan for this phase should be dedicated to finalizing incident documentation, including any official reports required by regulation or law. The plan should also include steps for integrating hardening techniques to prevent similar incidents, and a process for a lessons-learned analysis to enhance future incident response capabilities.
Incident Response Plan Testing
Another vital part of an incident response planning is testing. Testing an incident response plan can be as simple as a tabletop walkthrough, or as complex as third-party penetration testing. Ideally, more than one method of testing is utilized. Testing the incident response plan will help an organization identify critical gaps in the incident response plan before they become a major handicap during a live incident wreaking havoc on an environment. Something as simple as outdated contact information, or faulty equipment can give needless time to a threat causing exponential damage with each passing moment.
Contact Us
Contact 38North to learn more about how you can develop an incident response plan to not only meet requirements, but to safeguard your business.





